
Forbes has launched an online submissions system to allow the secure and anonymous submission of files and tip-offs from sources.
The system, called SafeSource, uses a combination of PGP encryption and web browser Tor to hide the content and identity of sources providing potentially sensitive information.
"In the past couple of years we've seen a big increase in the number of sources to the media that have been prosecuted," Andy Greenberg, a technology reporter for Forbes who helped implement SafeSource, told Journalism.co.uk.
"We realised that we need to find something better," he said.
Rather than using email to send files or tips, sources visit Forbes's SafeSource website using Tor, where they can upload files or leave messages that are automatically encrypted using PGP encryption.
"The two combined is a kind of end-to-end secrecy that includes identities too," said Greenberg. "We can have this two-way conversation with someone without knowing who they are or exposing their communications to eavesdropping."
Tor protects anonymity by passing encrypted communications through three of thousands of "nodes" provided by volunteer computers or servers, said Greenberg.
At present, only Greenberg and his colleague Nathan Vardi can access the encrypted files using their private PGP encryption key, after SafeSource encrypts the uploaded material.
Greenberg said all files and messages will be transferred to an unplugged, offline machine before they are decrypted to ensure there is no possibility of third-party access. Once there, they will be "scrubbed" of any metadata in the files that could identify the source.
"It may be that there are sources that are looking for someone to talk to but they feel that they need an extra layer of security," Greenberg said, "and we are trying to attract them".
"We're trying to get those stories that we may not be getting now but we're also responding to a new level of surveillance that's increasing."
The ongoing revelations form the leaked NSA files have uncovered the lengths to which online communications are being monitored by security services, but the Guardian's Glenn Greenwald almost lost the story when he dismissed Edward Snowden's initial request for PGP encrypted communications.
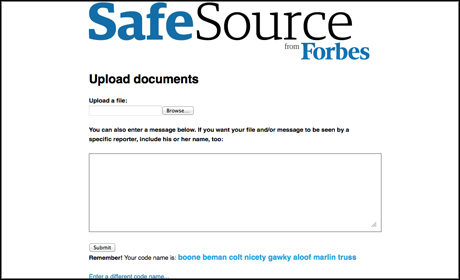
Screenshot from SafeSource
Unlike "a one-way upload system", SafeSource can potentially provide organisations with more scope for communication with a source, Greenberg said, through the use of a "passphrase".
Users are assigned a random passphrase of four to 10 words which they can use to log in to SafeSource and check for messages from Greenberg or Vardi, remaining anonymous as long as they do not reveal their passphrase or identity as a source, like Snowden chose to do.
"For stories we might have done in the past, just over anonymous emails, we're now realising that maybe that's not a secure enough way to communicate with our sources," said Greenberg, "and we need to provide them with something better as the surveillance tools of those who would want to expose sources increases – as those surveillance mechanisms – become more powerful."
On a smaller scale, the Cumberland and Westmorland Herald reported in April that local police and crime commissioner Richard Rhodes had spent £700 of public money on hiring a chauffeur-driven Mercedes after the newspaper received photocopied invoices in the post. Irene Brown, who sent the documents anonymously, was arrested and investigated for six months but was never charged of a crime. She has since spoken about the incident publicly to the newspaper.
SafeSource is based on an open-source framework for anonymous and secure communications called SecureDrop, itself based on code developed by Aaron Swartz and James Dolan called DeadDrop. Conde Nast hired Swartz and Dolan to build DeadDrop as a foundation for the New Yorker's StrongBox system, a similar platform to SecureDrop, launched in May.
In early October, the Freedom of the Press Foundation "upgraded and security audited" DeadDrop to create SecureDrop, said Greenberg, and released it publicly on GitHub and through the foundation's website.
Free daily newsletter
If you like our news and feature articles, you can sign up to receive our free daily (Mon-Fri) email newsletter (mobile friendly).









